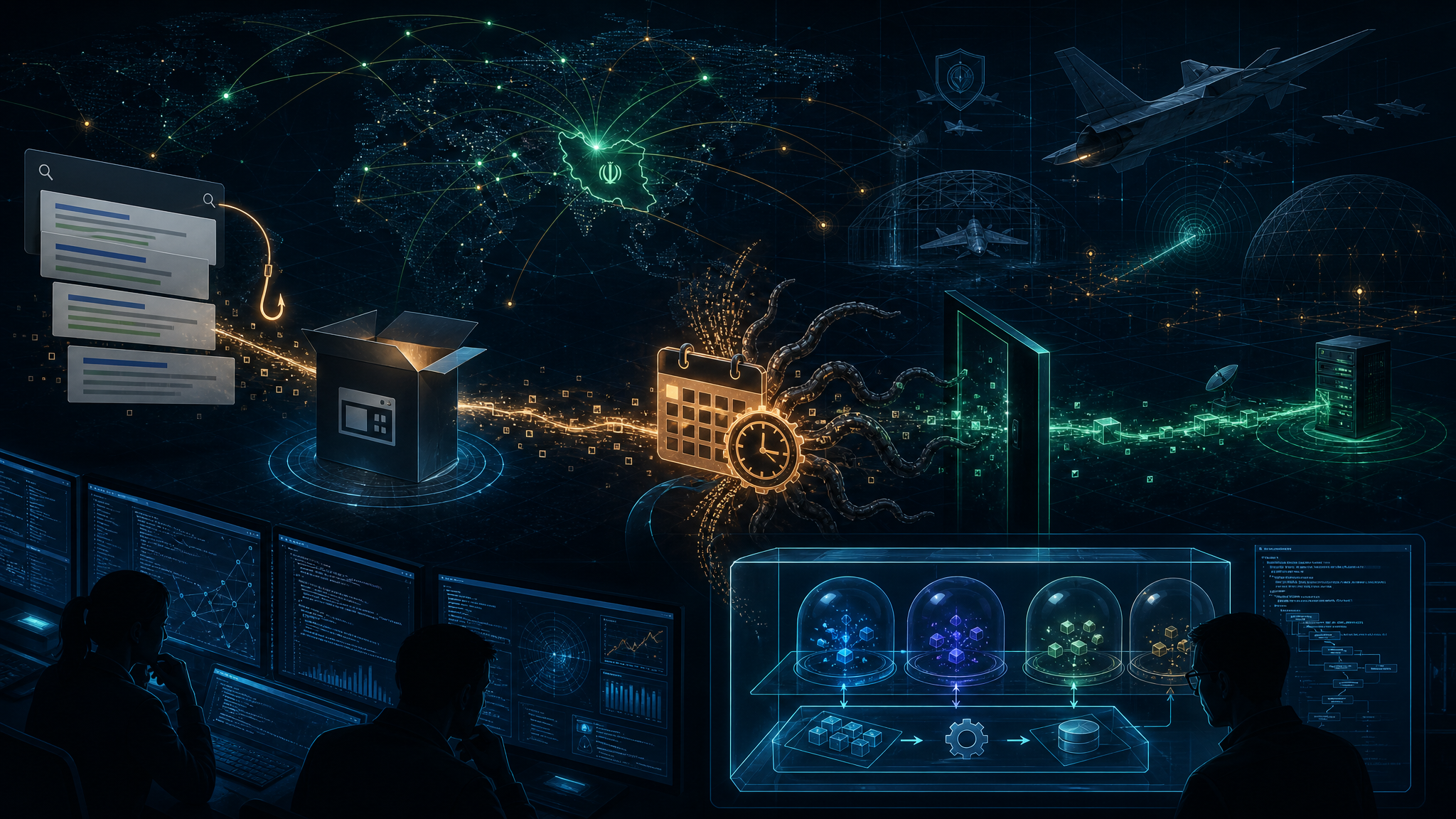
As Iran-Israel-US military operations escalate in the Middle East, Check Point Research and Tenable have identified a significant surge in Iranian threat actors targeting IP cameras manufactured by Hikvision and Dahua. The activity, which began spiking on February 28, 2026, coincides with the start of Operation Epic Fury and extends across Israel, Qatar, Bahrain, Kuwait, the UAE, Cyprus, and Lebanon.
Surveillance as a Weapon of War
The targeting campaign is not random opportunism—it appears to be systematic reconnaissance and battle damage assessment (BDA) support for kinetic military operations. Check Point researchers identified attack infrastructure that combines commercial VPN exit nodes (Mullvad, ProtonVPN, Surfshark, NordVPN) with virtual private servers, attributed to multiple Iranian-nexus threat actors.
The implications are chilling: by compromising security cameras near strategic targets, Iranian operators can observe locations before and after missile strikes, enabling real-time target correction and damage assessment. In one documented case during the June 2025 Israel-Iran conflict, Iran reportedly took control of a street camera facing the Weizmann Institute of Science just prior to striking it with a ballistic missile.
Exploited Vulnerabilities
The Iranian operators are exploiting known vulnerabilities in Hikvision and Dahua devices, several of which have been added to CISA’s Known Exploited Vulnerabilities (KEV) Catalog:
- CVE-2017-7921 — Hikvision IP Camera Improper Authentication (CVSS 10.0)
- CVE-2021-36260 — Hikvision Web Server Command Injection (CVSS 9.8)
- CVE-2021-33044 — Dahua Authentication Bypass (CVSS 9.8)
- CVE-2023-6895 — Hikvision Intercom Broadcasting System Command Injection (CVSS 9.8)
- CVE-2025-34067 — Hikvision Integrated Security Management Platform RCE (CVSS 9.8)
Patches are available for all listed vulnerabilities, but many organizations have not applied them, leaving cameras exposed to exploitation.
Activity Correlated with Geopolitical Events
Check Point’s deep-dive analysis revealed waves of camera-targeting activity that align closely with geopolitical flashpoints:
- January 14-15: Surge during Iran’s internal protests when Iranian officials anticipated potential U.S. strikes and closed airspace
- January 24: CENTCOM commander visited Israel and met with IDF Chief of Staff
- Early February: Iran’s leadership increasingly worried about imminent U.S. military action
- February 28: Sharp spike coinciding with the start of Operation Epic Fury
This pattern suggests that camera-targeting activity from Iranian infrastructure may serve as an early warning indicator of follow-on kinetic operations.
Recommendations for Defenders
Organizations with IP cameras—particularly those in Israel, Gulf states, or with ties to defense, critical infrastructure, or government—should take immediate action:
- Eliminate public exposure: Remove direct WAN access to cameras and NVRs; place them behind VPN or zero-trust access gateways
- Patch immediately: Apply firmware updates for all listed CVEs; replace end-of-life devices
- Enforce strong credentials: Change default passwords and enforce unique credentials per device
- Network segmentation: Isolate cameras on dedicated VLANs with no lateral access to corporate or OT networks
- Monitor for anomalies: Watch for repeated login failures, unexpected remote logins, and unusual outbound connections from camera devices
The Bigger Picture
This campaign demonstrates how cyber operations have become an integral component of modern warfare. Iranian threat actors aren’t just stealing data—they’re building real-time intelligence capabilities that directly support kinetic military operations. The convergence of cyber reconnaissance and physical strikes represents a new frontier in hybrid warfare that defenders must account for.
Organizations should review Tenable’s Operation Epic Fury threat brief and the IT-ISAC’s joint advisory for additional guidance on defending against Iranian threat actors.