
PawsRunner Steganography Shows Infostealers Are Hiding in Plain Sight
FortiGuard Labs reports PureLogs is being delivered through PawsRunner steganography. Here is what SMBs and government contractors should watch for defensively.

FortiGuard Labs reports PureLogs is being delivered through PawsRunner steganography. Here is what SMBs and government contractors should watch for defensively.

Unit 42 reports Gremlin Stealer has evolved with resource-file obfuscation, session hijacking, Discord token theft, and crypto clipboard fraud. Here is what SMBs and government contractors should do defensively.

Microsoft reports that Kazuar, attributed to Russian state actor Secret Blizzard, has evolved into a modular P2P botnet. Here is what SMBs and government contractors should take from it defensively.

Check Point’s look inside The Gentlemen ransomware operation is a useful reminder for SMBs and government contractors: exposed edge appliances, weak identity controls, and unmanaged remote access paths still drive real ransomware risk.
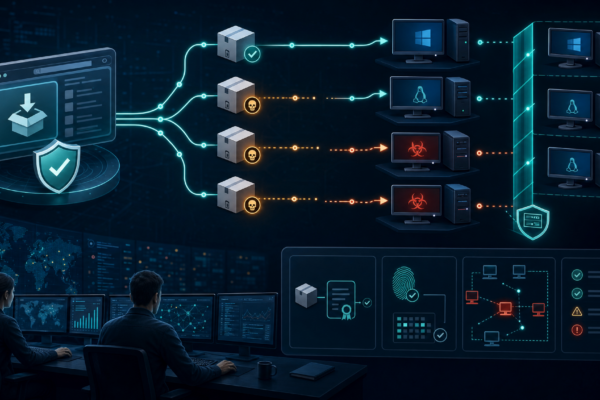
Attackers swapped selected JDownloader website download links with malicious installers. Here is what SMB and government-contractor defenders should do about trusted-download risk.

A fake OpenAI Privacy Filter repository on Hugging Face delivered Windows infostealer malware. Here is what SMB and gov-contractor defenders should take from it.

SentinelLabs reported PCPJack, a cloud-focused worm that evicts TeamPCP artifacts, steals credentials from exposed infrastructure, and spreads across cloud systems.

Kaspersky researchers have uncovered CrystalX RAT, a sophisticated new malware-as-a-service (MaaS) platform that combines remote access trojan capabilities with data theft, keylogging, and uniquely disturbing prankware features designed to psychologically torment victims. From Webcrystal to CrystalX: The Evolution First observed in January 2026 as Webcrystal RAT, the malware was initially promoted through private Telegram groups….

A sophisticated supply chain attack has compromised LiteLLM, the widely-used Python library for interfacing with large language models, delivering multi-stage credential-stealing malware to systems downloading over 95 million packages per month. The attack, attributed to TeamPCP—the same threat group behind the recent Trivy supply chain compromises—targeted LiteLLM versions 1.82.7 and 1.82.8 on PyPI. According to…

On March 31, 2026, the cybersecurity landscape was shaken by a significant supply chain attack targeting Axios, one of the most widely used HTTP client libraries in the JavaScript ecosystem with over 83 million weekly downloads. Attackers compromised a maintainer account to inject a cross-platform remote access trojan (RAT) into two malicious package versions. Attack…