APT36 Vibeware Campaign: Pakistan’s Transparent Tribe Weaponizes AI to Mass-Produce Malware Targeting India
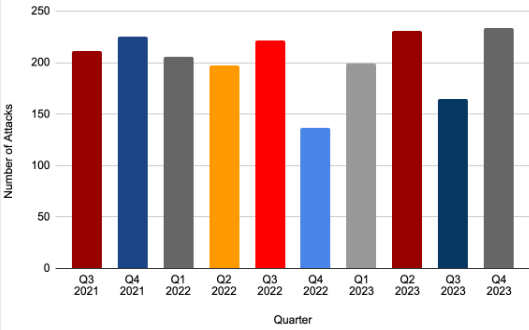
Pakistan-aligned threat actor Transparent Tribe (APT36) has embraced AI-assisted malware development to flood Indian government networks with disposable, polyglot implants—a technique security researchers are calling “vibeware” or Distributed Denial of Detection (DDoD). AI-Powered Malware Industrialization According to Bitdefender’s research, APT36 has shifted from sophisticated, handcrafted implants to high-volume, AI-generated malware written in obscure programming languages…