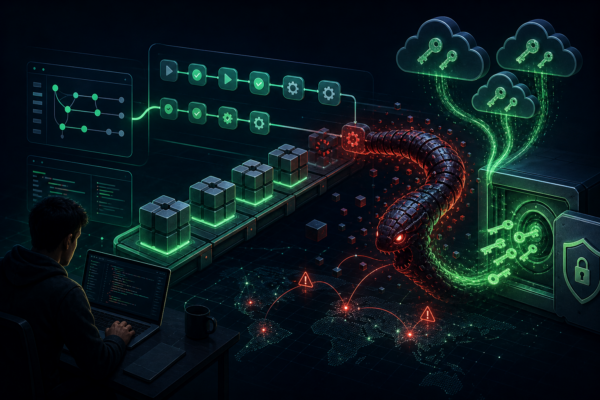
Red Hat’s Miasma npm Compromise Shows Trusted Publishing Is Not a Control Boundary
A Red Hat Cloud Services npm compromise shows why signed releases and trusted publishing must be paired with install-time controls, CI/CD isolation, and fast credential rotation.









