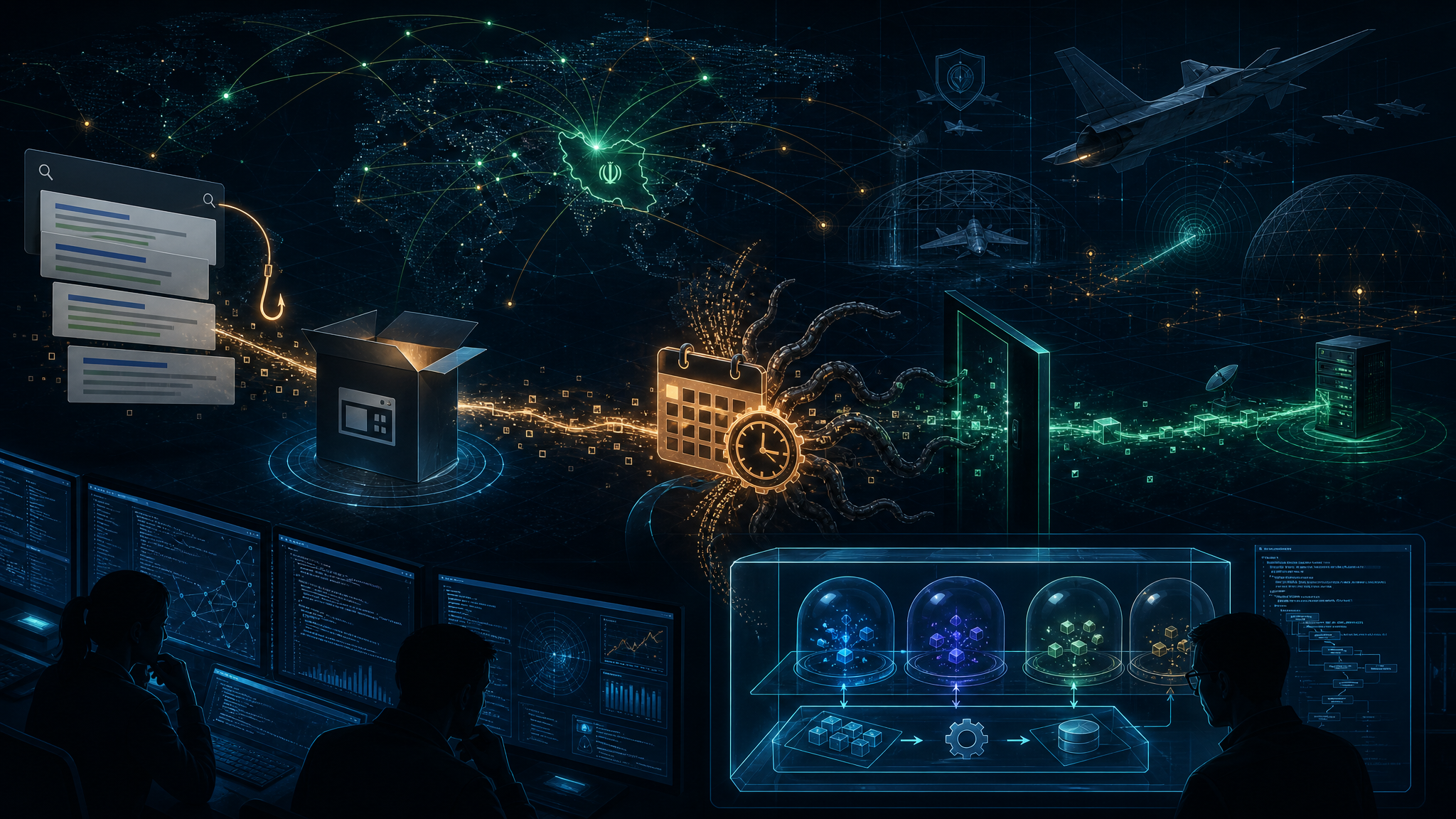
A comprehensive analysis by Unit 42 reveals a fundamental shift in Iranian cyber operations: state-aligned threat actors are abandoning custom malware in favor of weaponizing enterprise administrative tools to achieve unprecedented scale and stealth.
The Strategic Shift
During recent wiper incidents attributed to Void Manticore (Handala), attackers did not deploy novel malware or traditional compiled binaries. Instead, they compromised highly privileged identities and pushed legitimate remote-wipe commands via mobile device management (MDM) platforms—simultaneously wiping over 200,000 devices globally.
This “identity weaponization” approach offers critical advantages:
- EDR Blindspot: No malware is dropped, no anomalous disk-writing processes trigger alerts—the destructive commands are authenticated, authorized, and delivered from trusted vendor infrastructure
- Unprecedented Scale: A single compromised admin credential can wipe hundreds of thousands of corporate laptops, servers, and mobile devices across global environments
- Resource Efficiency: Eliminates the need to develop, test, and update custom malware families
A Decade of Evolution
Unit 42 traces a clear escalation pattern among IRGC and MOIS-linked groups:
2016-2019: The Blunt Instruments
Groups like APT33 (Curious Serpens) and APT34 (Evasive Serpens) deployed high-visibility disk-wiping malware. Shamoon 2 and 3, ZeroCleare, and Dustman used legitimate drivers to overwrite master boot records (MBRs), prioritizing visible retaliation over stealth.
2020-2022: Ransomware Smokescreens
Agrius (Agonizing Serpens) pioneered plausible deniability by disguising wiper operations as ransomware attacks. Early versions of the Apostle wiper lacked actual decryption capability—data destruction was the true intent. The Fantasy wiper escalated further via a supply-chain attack compromising a trusted Israeli software developer.
2023-2025: Hacktivism as Cover
State-directed hacktivist personas emerged, including Void Manticore and Handala Hack Team. Cross-platform wipers like BiBi, Hatef, and Hamsa targeted both Windows and Linux environments. Collaborative operations between Agrius and MuddyWater deployed modular wipers using legitimate RMM tools for distribution.
2026 and Beyond: Identity Weaponization
The current era represents a fundamental departure. Iranian APTs now view enterprise administrative tools—particularly MDM and cloud management consoles—not as IT infrastructure, but as weaponizable assets that bypass traditional endpoint detection entirely.
Why This Matters
For the IRGC and MOIS, cyber operations provide a low-cost, high-impact mechanism for retaliation without crossing geographical boundaries. The shift from custom malware to native administrative abuse removes a critical detection guardrail that historically protected enterprise networks.
Critical implication: An organization’s infrastructure is only as strong as its weakest administrative credential.
Defensive Countermeasures
Unit 42 recommends:
- Treat management platforms as Tier-0: MDM policy changes and role assignments require the same rigor as domain controller modifications
- Enforce strict Zero Trust: Access to admin portals must require verification from known, compliant corporate devices—not just MFA
- Eliminate standing privileges: Implement Just-In-Time (JIT) privileged access with approval workflows
- Air-gap backups: Offline, immutable backups are non-negotiable when the cloud tenant itself may be compromised
For the full technical analysis and historical timeline, see the complete Unit 42 report.