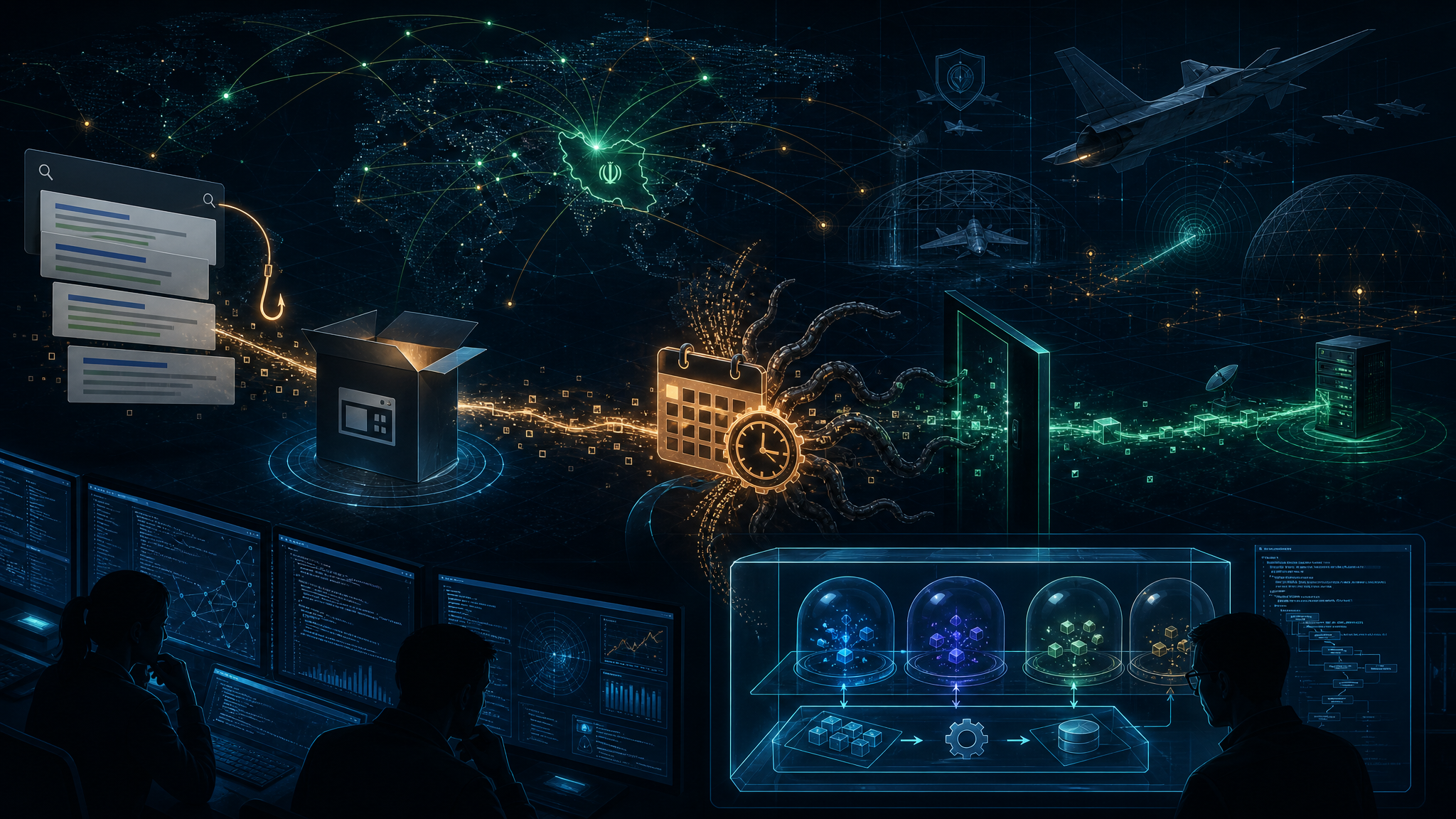
A cybercrime group is attempting to leverage the ongoing US-Iran conflict by deploying a destructive wiper malware that specifically targets systems configured for Iranian users, according to new research from Krebs on Security and Aikido.
TeamPCP Launches Iran-Targeting Wiper
The financially motivated threat actor TeamPCP has weaponized its existing supply chain compromise to deploy CanisterWorm, a wiper that identifies and destroys data on systems matching Iran’s timezone or configured with Farsi as the default language.
Security researcher Charlie Eriksen from Aikido reports that if the wiper detects a victim in Iran with access to a Kubernetes cluster, it will systematically destroy data on every node in that cluster. Systems without Kubernetes access simply have their local data wiped.
Blockchain-Based Command Infrastructure
TeamPCP’s infrastructure—dubbed CanisterWorm by researchers—leverages the Internet Computer Protocol (ICP), a blockchain-based system of tamperproof “smart contracts” that combine code and data. These canisters can serve web content directly and their distributed architecture makes them highly resistant to takedown attempts.
“The canisters will remain reachable so long as their operators continue to pay virtual currency fees to keep them online,” Krebs noted.
Supply Chain Attack Chain
The Iran-targeting payload emerged from TeamPCP’s March 19 supply chain attack against Trivy, the popular vulnerability scanner from Aqua Security. The attackers injected credential-stealing malware into official GitHub releases, capturing SSH keys, cloud credentials, Kubernetes tokens, and cryptocurrency wallets.
According to Wiz, TeamPCP has now expanded operations to compromise the KICS vulnerability scanner from Checkmarx, with the GitHub Action compromised between 12:58 and 16:50 UTC on March 23rd.
Chaotic Tactics
TeamPCP’s operators have demonstrated erratic behavior, toggling their malicious canisters between serving malware and redirecting to Rick Roll videos on YouTube. They’ve also been spotted bragging about their exploits in Telegram groups and spamming compromised GitHub accounts to demonstrate their access.
“It’s a little all over the place, and there’s a chance this whole Iran thing is just their way of getting attention,” Eriksen told Krebs. “I feel like these people are really playing this Chaotic Evil role here.”
Why It Matters
As tensions between the US and Iran escalate, opportunistic threat actors are injecting themselves into the conflict—regardless of whether their attacks cause meaningful damage. The Iran-focused wiper payload emerged during Iran’s ongoing internet restrictions following recent demonstrations, potentially limiting its actual impact.
For organizations using Trivy or KICS in their CI/CD pipelines, immediate review of credentials and tokens is critical. Teams should verify they’re using clean versions of these tools and rotate any potentially compromised secrets.