Source: Microsoft Security Blog
Microsoft is tracking active exploitation around a newly disclosed Linux local privilege escalation issue being called Dirty Frag. The important part for defenders is not just “another Linux kernel bug.” It is the role this class of vulnerability plays after the attacker already has a foothold.
Dirty Frag is reported to involve vulnerable Linux kernel networking and memory-fragment handling paths, including esp4, esp6 / xfrm components tied to IPsec-style functionality, and rxrpc. Microsoft identifies related CVEs as CVE-2026-43284 and CVE-2026-43500. In practical terms, successful exploitation may allow a low-privileged local user or process to become root.
Why this matters
Local privilege escalation does not usually create the first breach. It makes the breach worse.
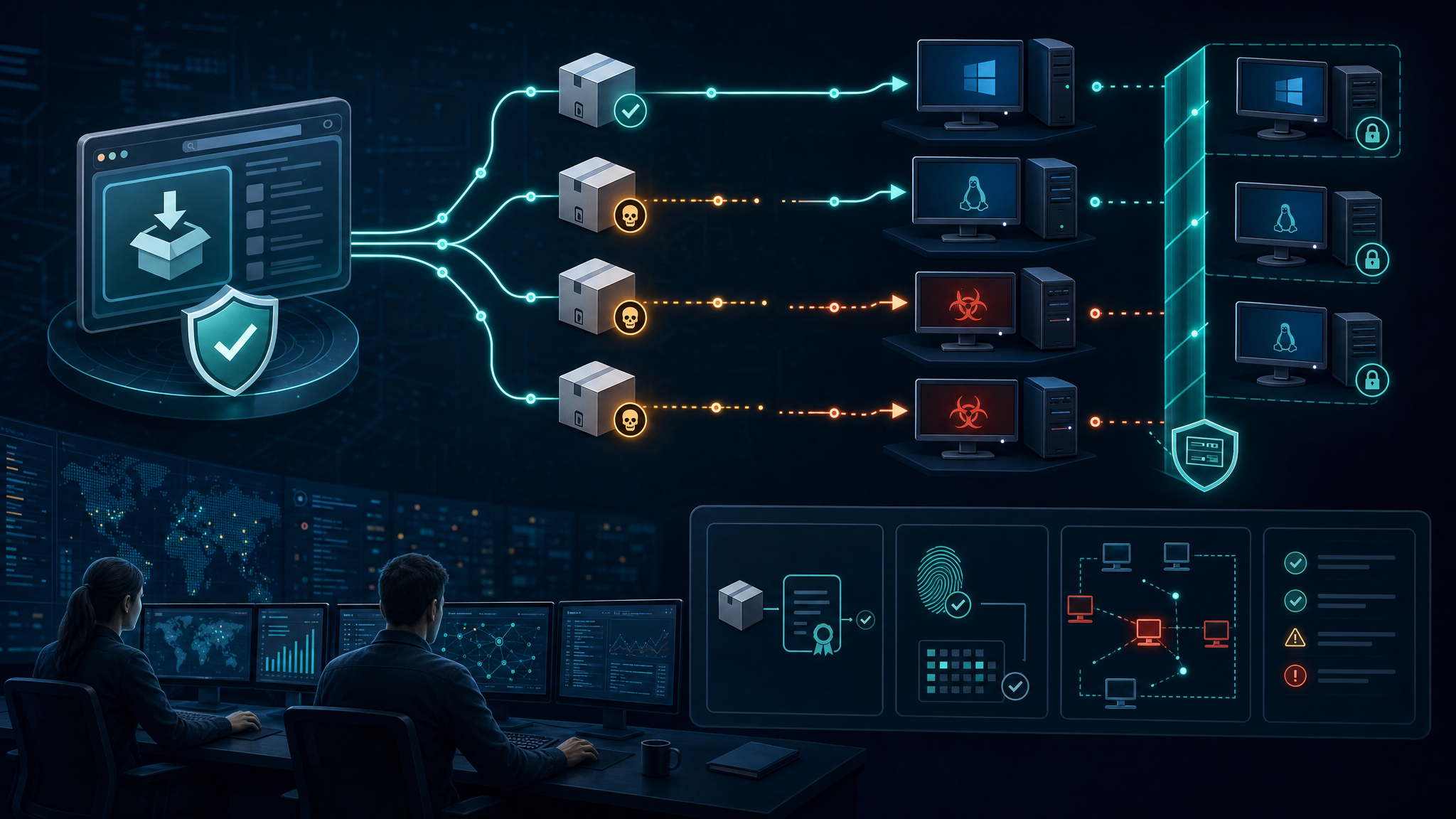
If an attacker gets limited execution through a stolen SSH credential, a vulnerable web application, a web shell, a container workload, or a low-privileged service account, a reliable privilege escalation path can turn that limited access into control of the host. Once root is obtained, the attacker can disable security tools, collect credentials, tamper with logs, persist more deeply, and pivot into adjacent systems.
That is why Dirty Frag deserves attention from SMBs, managed service providers, and government contractors running Linux infrastructure. The risk is highest where Linux hosts are internet-adjacent, container-heavy, lightly monitored, or treated as “set and forget” appliances.
Systems to prioritize first
- Internet-facing Linux servers, especially VPN, reverse proxy, application, and SSH-accessible hosts.
- Container hosts and OpenShift/Kubernetes worker nodes where a container escape or weak workload boundary could expose the host kernel.
- Servers using IPsec, xfrm, esp4, or esp6 functionality, because emergency module changes may affect production networking.
- Hosts with many local users or service accounts, including shared admin boxes and build systems.
- High-value Linux systems holding credentials, CI/CD secrets, logs, backups, or sensitive customer data.
Immediate defensive actions
- Inventory affected Linux kernels and distributions. Track Ubuntu, RHEL, CentOS Stream, AlmaLinux, Fedora, openSUSE, OpenShift, and any custom appliance kernels separately.
- Monitor vendor advisories and patch quickly. Kernel fixes should be treated as priority maintenance, not routine backlog work.
- Review whether rxrpc and IPsec/xfrm-related modules are needed. If they are unused, consider disabling or preventing load of risky modules after testing. Do not blindly disable IPsec-related components on VPN-dependent systems.
- Reduce local execution paths. Tighten SSH access, remove stale accounts, restrict shells for service users, and review sudo rules.
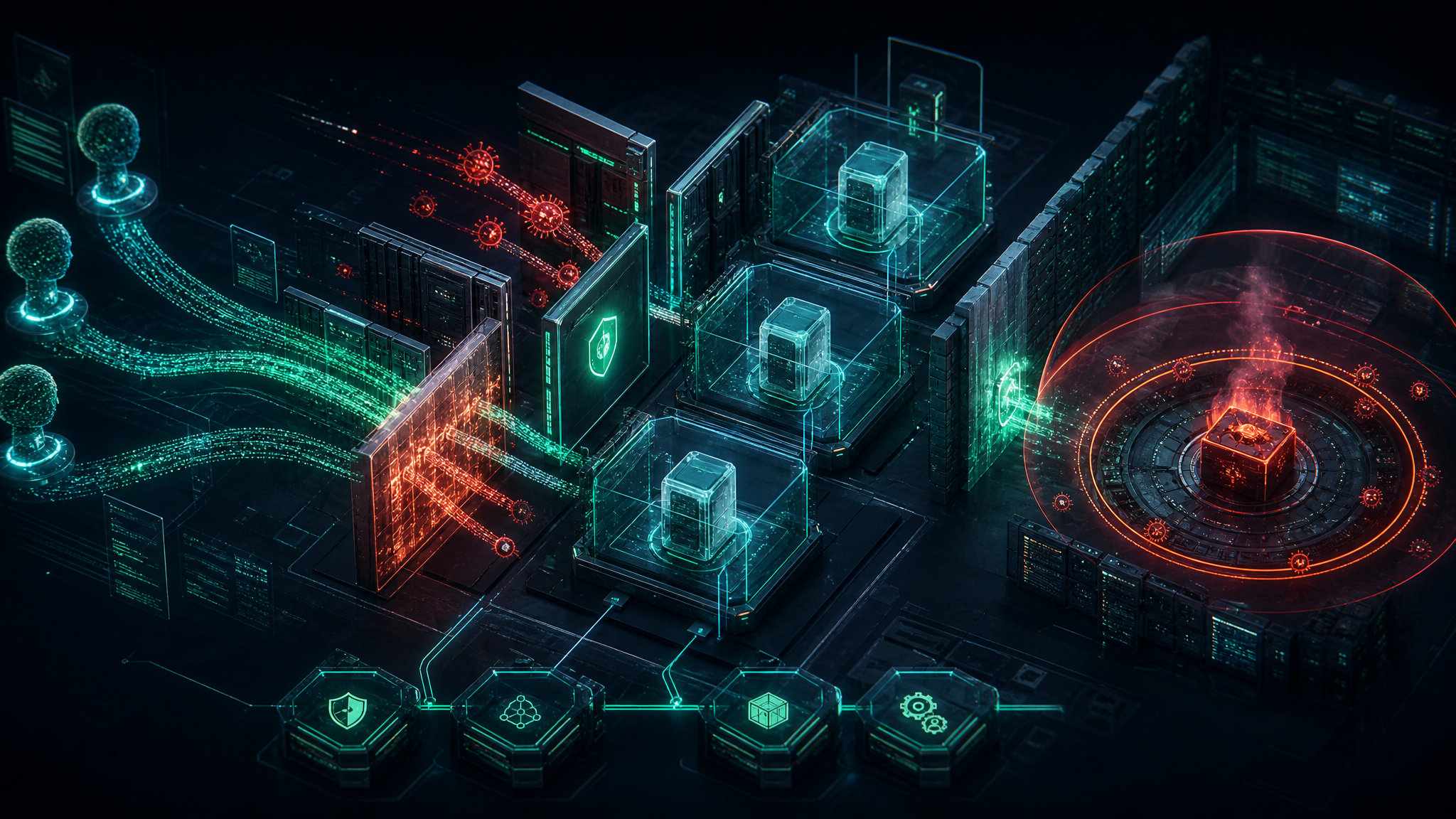
- Harden container boundaries. Use seccomp/AppArmor/SELinux where available, avoid privileged containers, limit hostPath mounts, and keep container hosts patched ahead of general-purpose servers.
- Increase post-exploitation monitoring. Watch for unusual root process creation, kernel module loading, suspicious writes around setuid binaries, security tool tampering, credential access, and log clearing.
Detection ideas for small teams
You do not need a giant SOC to get value here. Start with a few high-signal checks:
- Alert when a low-privileged account suddenly spawns root shells or root-owned processes outside normal sudo workflows.
- Review recent SSH logins, especially from unfamiliar networks or service accounts.
- Look for new persistence under
/etc/systemd/system, cron paths, shell profiles, and user SSH authorized keys. - Compare endpoint telemetry before and after patching for stopped agents, disabled EDR services, or abnormal kernel module activity.
- If Microsoft Defender is deployed on Linux, review detections associated with Dirty Frag exploitation and related post-compromise behavior.
Operational caution
Emergency mitigations that unload or block kernel modules can break legitimate services. Treat these as change-controlled actions, especially on VPN, IPsec, storage, identity, and clustered systems. The safer path is usually: identify exposure, test module mitigations on non-production or lower-risk systems, patch as vendor updates arrive, and monitor for exploitation indicators in parallel.
Also remember that privilege escalation may leave behind changes that patching alone will not remove. If there is evidence of exploitation, perform incident response: preserve logs, isolate the host if needed, rotate credentials that touched the system, validate file integrity, and rebuild from trusted images when confidence is low.
Bulwark Black takeaway
Dirty Frag is a reminder that Linux hardening is not just about blocking initial access. For contractors and small businesses, the real defensive win is reducing the blast radius after one account, container, or web app gets popped. Patch the kernel, limit local execution, harden containers, and make privilege escalation noisy enough that it gets caught early.