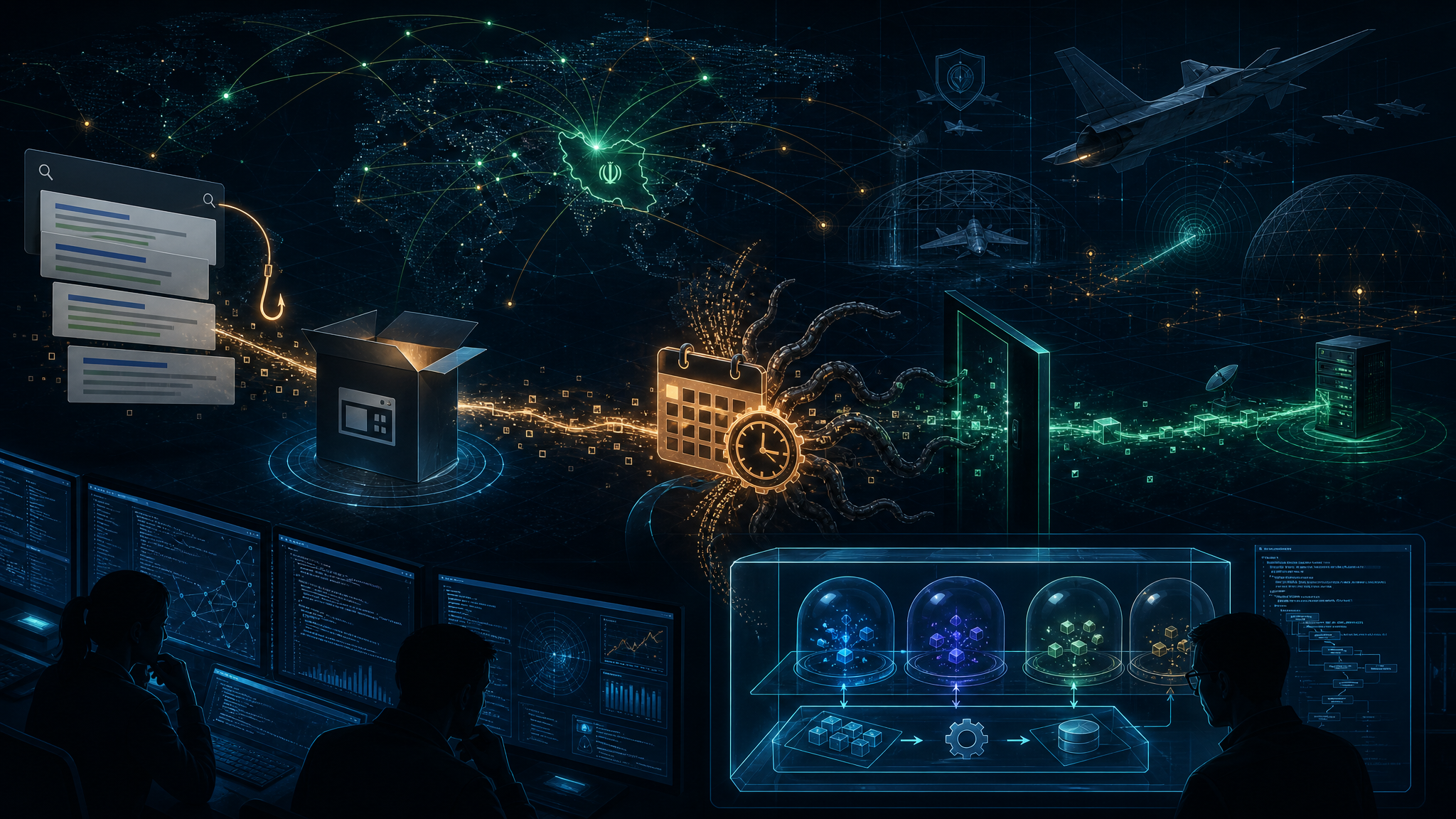
The FBI has issued a flash alert warning network defenders that Iranian hackers linked to the Ministry of Intelligence and Security (MOIS) are actively using Telegram as command-and-control (C2) infrastructure in malware attacks targeting journalists, dissidents, and opposition groups worldwide.
Threat Actor Profile
The bureau attributed these attacks to two Iranian-linked threat groups:
- Handala (also known as Handala Hack Team, Hatef, Hamsa) — A pro-Palestinian hacktivist group linked to Iranian intelligence
- Homeland Justice — A state-sponsored threat group tied to Iran’s Islamic Revolutionary Guard Corps (IRGC)
Attack Methodology
According to the FBI, these Iranian threat actors are leveraging social engineering to deploy Windows malware capable of:
- Exfiltrating screenshots from compromised systems
- Stealing files from targeted computers
- Using Telegram channels for C2 communication
The malware has resulted in intelligence collection, data leaks, and reputational harm against targeted parties.
Recent Law Enforcement Action
This warning follows the FBI’s seizure of four domains used by the threat groups:
- handala-redwanted[.]to
- handala-hack[.]to
- justicehomeland[.]org
- karmabelow80[.]org
These websites were used to leak sensitive documents and data stolen from victims in the United States and globally. The seizures came in the wake of Handala’s devastating attack on U.S. medical device giant Stryker, where approximately 80,000 devices were factory reset using compromised Microsoft Intune administrator credentials.
Why This Matters
The FBI explicitly noted the “elevated geopolitical climate of the Middle East and current conflict” as the impetus for this warning. With ongoing US-Iran tensions, organizations should expect continued targeting by Iranian cyber actors.
The use of Telegram as C2 infrastructure demonstrates how threat actors continue to abuse legitimate platforms to evade detection. Network defenders should monitor for unusual Telegram API activity from corporate networks.
Recommended Mitigations
- Monitor for suspicious Telegram-related network traffic
- Implement robust email security to prevent social engineering
- Review Microsoft Intune and Azure AD configurations for unauthorized administrator accounts
- Enable MFA across all administrative accounts
- Segment networks to limit lateral movement