Source article found in Feedly: SentinelLabs, “PCPJack | Cloud Worm Evicts TeamPCP and Steals Credentials at Scale.”
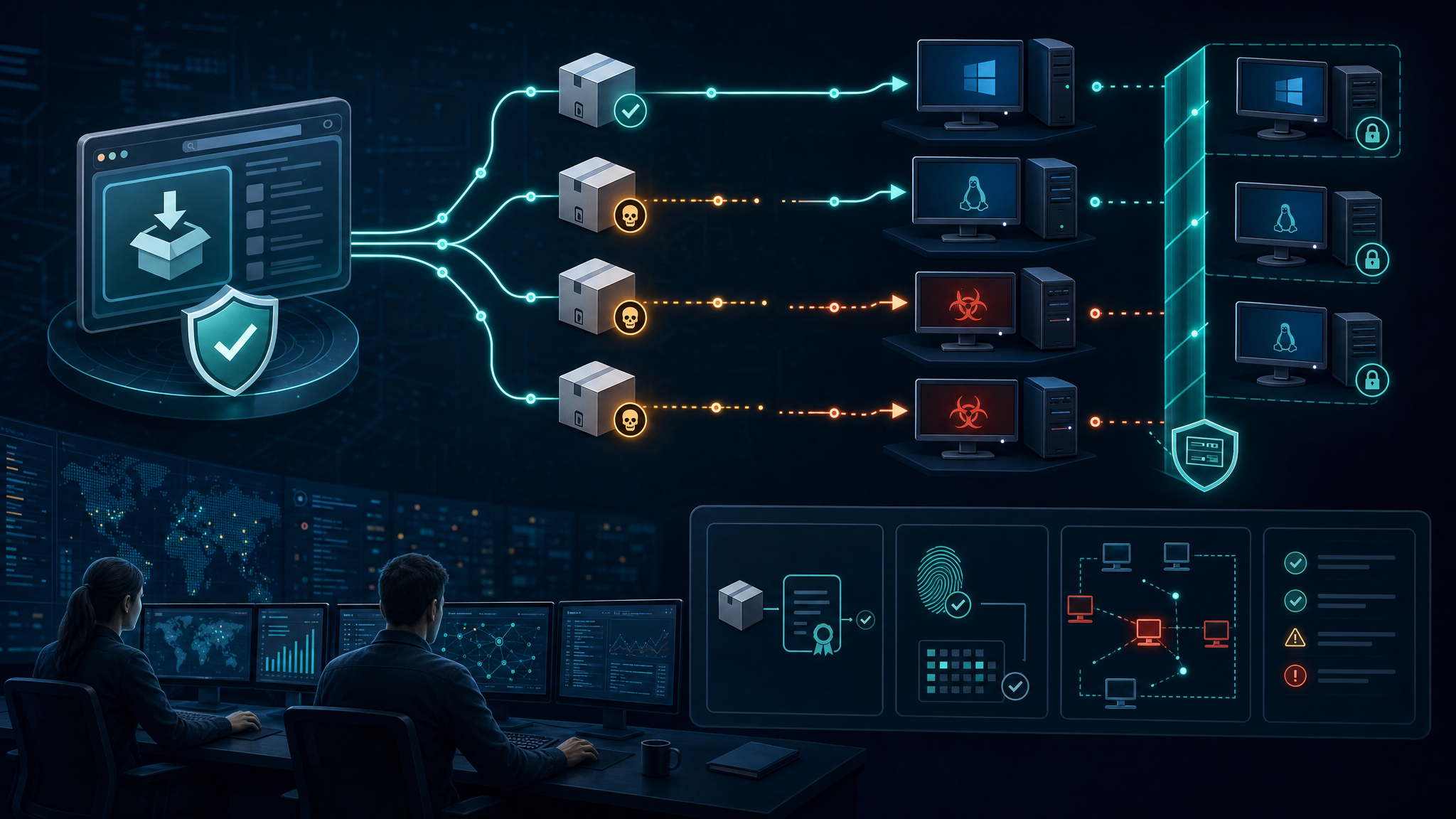
SentinelLabs has reported a cloud-focused credential theft framework called PCPJack that behaves more like a worm than a one-off intrusion script. The toolset targets exposed cloud and developer infrastructure, removes artifacts associated with the TeamPCP actor persona, harvests credentials, and attempts to propagate across additional systems.
The operational detail that stands out is the monetization model. This is not the usual “drop a cryptominer on an exposed Docker host” cloud compromise. SentinelLabs notes that PCPJack goes after credentials from cloud, container, developer, productivity, and financial services. That points toward fraud, spam, extortion, resale of access, or follow-on compromise rather than quick commodity mining.
What PCPJack Targets
According to SentinelLabs, PCPJack targets exposed services and environments including:
- Docker and Kubernetes infrastructure
- Redis and MongoDB instances
- RayML and vulnerable web applications
- Cloud metadata and service account credentials
- Developer secrets in configuration files, environment variables, Git history, and SSH material
- Cryptocurrency wallets and keys
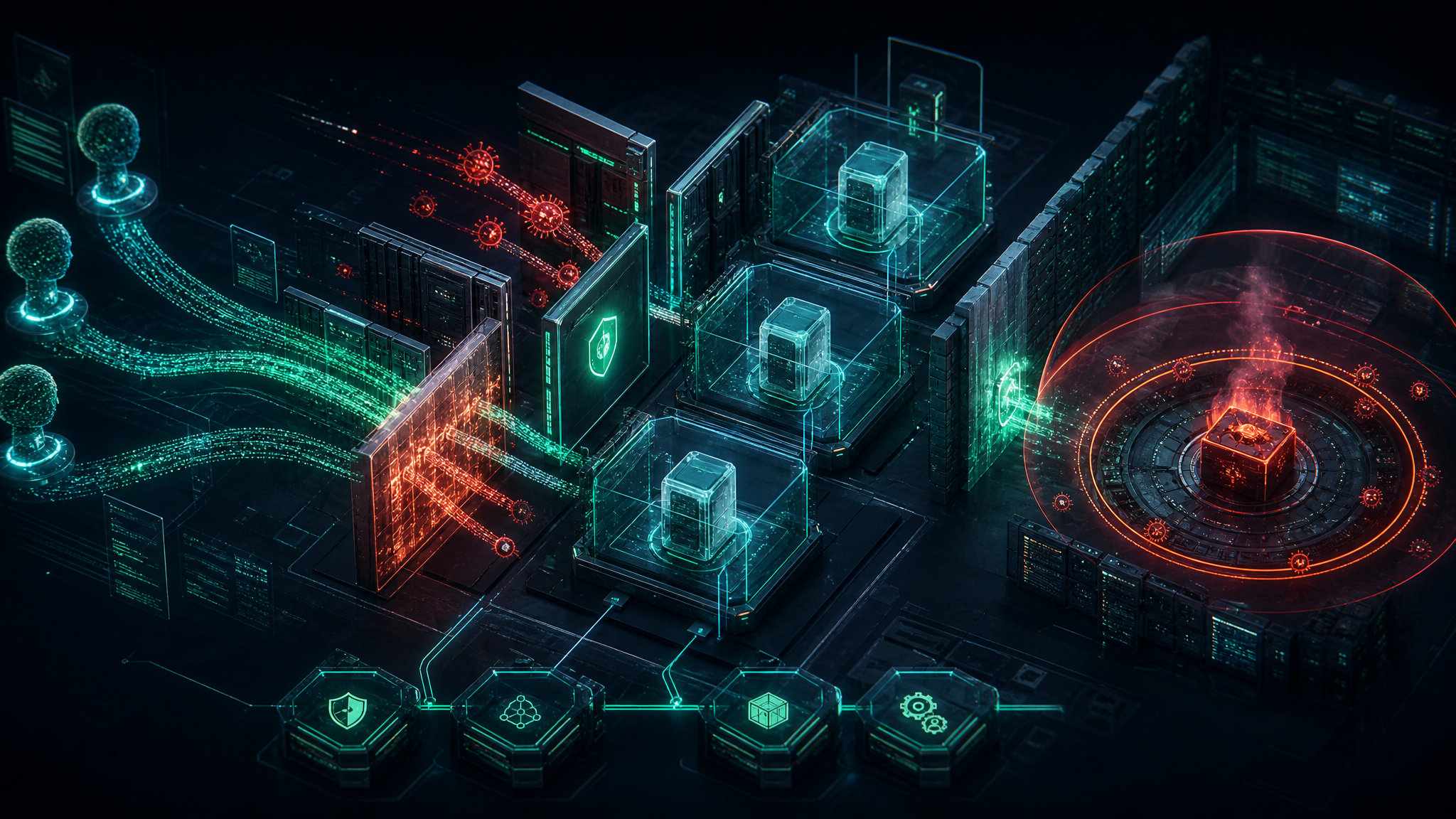
The framework includes a Linux bootstrap script, Python modules for credential parsing and lateral movement, cloud range scanning, and persistence mechanisms. It also attempts to remove rival TeamPCP-related tools before establishing itself.
Why This Matters
Cloud compromise is maturing. Attackers increasingly understand that the most valuable asset in a cloud environment is not always compute. It is the credential graph: API keys, service tokens, SSH keys, registry credentials, SaaS tokens, database secrets, and CI/CD access.
Once those credentials are collected, the attacker can often move far beyond the first exposed service. A single misconfigured container host can become access to source code, cloud storage, internal databases, Slack workspaces, payment systems, or production deployment pipelines.
Defensive Takeaways
- Find exposed services fast. Internet-facing Docker, Kubernetes dashboards, Redis, MongoDB, RayML, and similar services should be inventoried and locked down.
- Rotate secrets after compromise. Reimaging a host is not enough if environment variables, service account tokens, SSH keys, or cloud keys were exposed.
- Monitor for credential harvesting behavior. Alert on bulk access to
.envfiles, shell histories, Git repositories, service account paths, Docker secrets, and cloud metadata services. - Harden metadata access. Restrict access to cloud instance metadata services and enforce least privilege on attached roles.
- Watch for persistence. SentinelLabs observed systemd service creation for root execution and cron-based persistence when running without root.
- Treat cloud malware as access theft, not just resource theft. A missing cryptominer does not mean the incident is low impact.
Bulwark Black Assessment
PCPJack is a good example of where cloud threat activity is heading: less noisy mining, more credential collection, more lateral movement, and more monetization through stolen access. For defenders, the priority is to reduce exposed management surfaces, tighten identity controls, and make credential discovery noisy enough that it cannot happen quietly.
For small and mid-sized organizations, the practical starting point is simple: inventory internet-facing assets, verify cloud IAM scope, rotate old secrets, and monitor the places attackers actually search for credentials.
Source: SentinelLabs — PCPJack | Cloud Worm Evicts TeamPCP and Steals Credentials at Scale