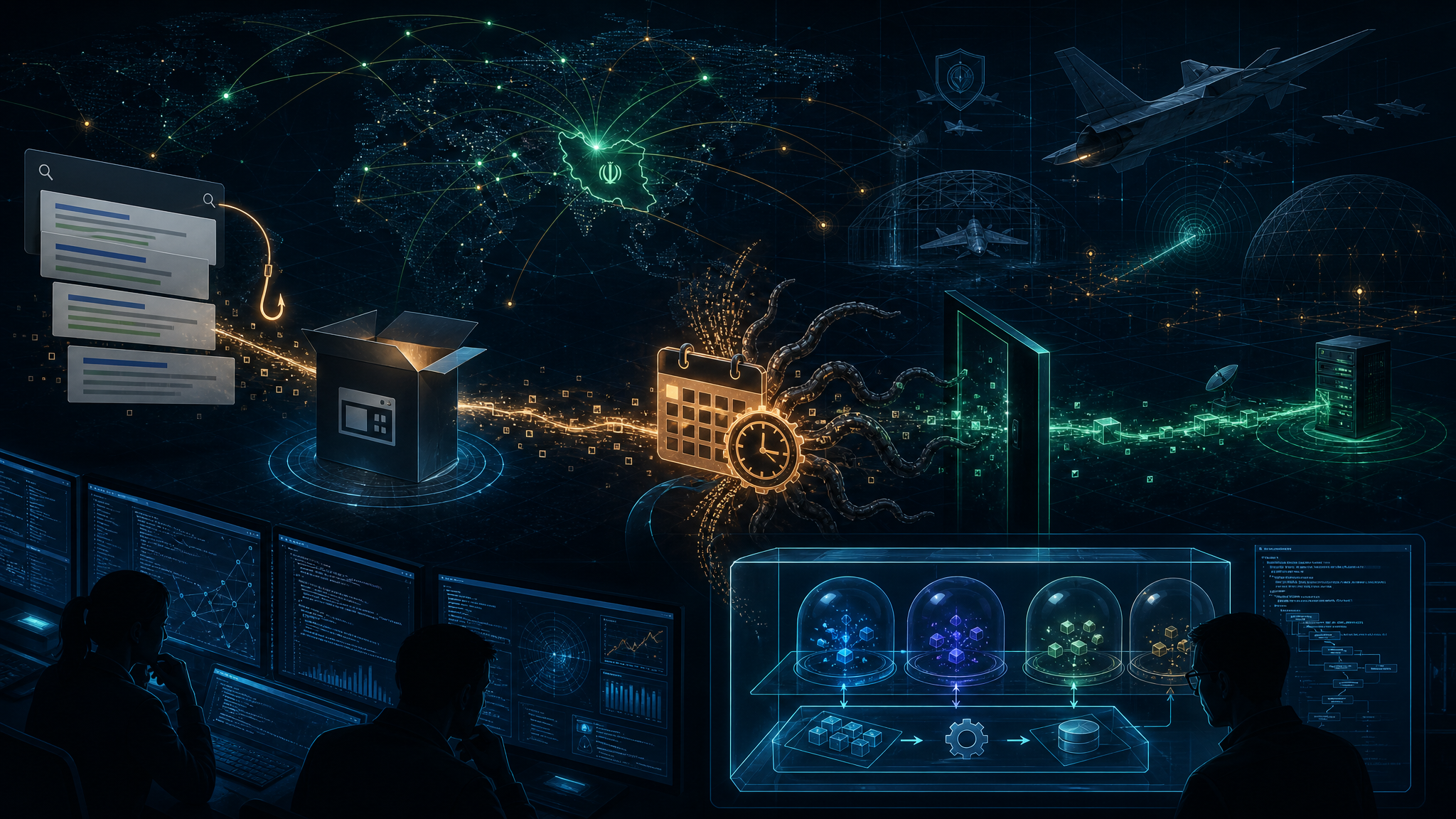
In the largest single-event activation of Iranian-aligned cyber actors ever documented, more than 60 pro-Iranian hacktivist groups became active on Telegram within hours of the February 28 US-Israel military strikes on Iran. Armed with AI tools and targeting over 40,000 internet-exposed control systems in the United States, these groups represent a dangerous new dimension of the cyber threat landscape.
The Scale of the Threat
According to CloudSEK researchers, these hacktivist groups are joining established nation-state actors like CyberAv3ngers, MuddyWater, Cotton Sandstorm, and Educated Manticore in targeting the United States, Israel, and regional allies. Unlike state-directed groups, these hacktivists operate on ideological grounds and have “no political constraint on civilian impact.”
The timing is significant: the Islamic Revolutionary Guard Corps (IRGC), which typically directs nation-state cyber operations, has been disrupted by the military strikes. This has created a decentralized threat environment where motivated hacktivists can operate with minimal oversight.
AI Collapses the Technical Barrier
What makes 2026 different from previous years is AI’s role in democratizing ICS attacks. CloudSEK researchers explain that attacking critical infrastructure traditionally required years of expertise in understanding industrial protocols, programmable logic controllers (PLCs), and specialized knowledge that limited such operations to nation-states.
AI has fundamentally changed this equation. As the researchers note: “To exploit internet-exposed ICS devices with default or absent credentials, you do not need to understand how a PLC works. You need to know it exists, where it is, and what password to type.” AI tools can now surface this information in a single conversation, compressing weeks of reconnaissance into minutes.
The OpenAI-DoD Factor
The connection between AI vendors and the Department of Defense adds another layer to this threat. In 2024, OpenAI reported that CyberAv3ngers accounts used ChatGPT for ICS reconnaissance—looking for industrial protocols, default credentials, and network scanning techniques. With AI assistance, these nation-state tactics can now be easily replicated by hacktivists.
Nation-State Activity Continues
Check Point researchers have documented Iranian groups infiltrating IP cameras across Israel, Bahrain, Qatar, and Kuwait—likely for damage assessment and target identification.
Symantec and Carbon Black have attributed ongoing activity on US company networks to Seedworm (also known as MuddyWater and Static Kitten), with campaigns that began in early February and have intensified since the air strikes.
Even Russian actors have entered the arena. NoName057, using the DDoSia toolkit, has partnered with Iranian counterparts to target Israeli defense, telecom, and infrastructure systems.
What Defenders Need to Know
Key threat actors to watch:
- CyberAv3ngers — Proven ICS targeting capability (Aliquippa water system compromise)
- Seedworm/MuddyWater — Active campaigns against US organizations
- Cotton Sandstorm — Influence operations and infrastructure targeting
- Educated Manticore — Espionage and reconnaissance
- Handala and Agrius — Wiper malware and destructive attacks
Defensive priorities:
- Audit internet-exposed ICS/SCADA systems immediately
- Change default credentials on all industrial control devices
- Implement network segmentation between IT and OT environments
- Monitor for reconnaissance activity targeting industrial protocols
- Review access logs for AI-assisted scanning patterns
Source: Security Boulevard