Business
Automating C2 Infrastructure with Terraform, Nebula, Caddy and Cobalt Strike
Read Article The ability to quickly build out a C2 infrastructure within a few minutes, including all the set up and tear down logic included would be a great asset for any offensive security group or operator. In this post, I will show exactly how to build a fully automated functional C2 infrastructure using Terraform, Nebula, Caddy and Cobalt Strike….

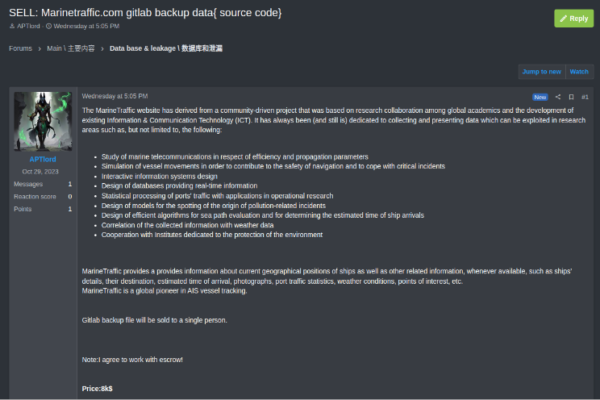
The Underground Economist: Volume 4, Issue 1
https://www.zerofox.com/blog/the-underground-economist-volume-4-issue-1/ On December 27, 2023, threat actor “APTlord” announced on the dark web forum RAMP that they were selling source code and other information owned by marinetraffic[.]com, which was allegedly obtained by the theft of backup data from web-based Git repository GitLab. Marinetraffic[.]com is an open-source analytics platform that provides real-time information on maritime vessels…

Red Pandas Unleashed: How Webhooks, Bad USB, and WiFi Collide in Cyberspace
Read Article The Power of Automation for Pentesting Automation has become a game-changer in the world of penetration testing. With the ever-increasing complexity of networks and systems, manually tracking and responding to security events is no longer viable. This is where webhooks come into play for cybersecurity professionals, and where we as pentesters can abuse…
- 1
- 2
