Malware

Hundreds of Thousands of Dollars Worth of Solana Cryptocurrency Assets Stolen in Recent CLINKSINK Drainer Campaigns
Read Article On January 3, 2024, Mandiant’s X social media account was taken over and subsequently used to distribute links to a cryptocurrency drainer phishing page. Working with X, we were able to regain control of the account and, based on our investigation over the following days, we found no evidence of malicious activity on,…

Custom GPTs: A Case of Malware Analysis and IoC Analyzing
Read Article On November 6, 2023, CustomGPTs, a new feature that OpenAI stated on its blog, became available. We can already say that the emergence of Custom Generative Pre-trained Transformers (GPTs) could mark a significant shift in the dynamics of both digital defense and offense. AI models, customizable for specific tasks, could represent a new frontier in…
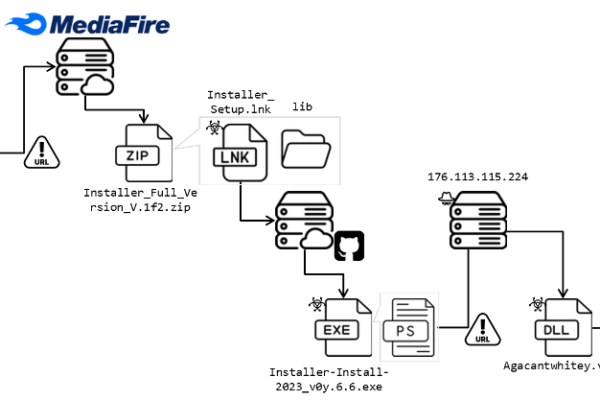
Deceptive Cracked Software Spreads Lumma Variant on YouTube
Read Article Initial Infection Vector The hacker initially breaches a YouTuber’s account and uploads videos masquerading as sharing cracked software. Figure 3 shows the video descriptions in which a malicious URL is embedded, enticing users to download a ZIP file that harbors malicious content for the next stage of the attack. The videos were uploaded…


AsyncRAT loader: Obfuscation, DGAs, decoys and Govno
Read Article Executive summary AT&T Alien Labs has identified a campaign to deliver AsyncRAT onto unsuspecting victim systems. During at least 11 months, this threat actor has been working on delivering the RAT through an initial JavaScript file, embedded in a phishing page. After more than 300 samples and over 100 domains later, the threat…
Chapter 84: In-depth analysis and technical analysis of LockBit, the top encryption ransomware organization (Part 1)
Read Article Excerpt LockBit operators and affiliates will find ways to obtain the victim’s initial access rights and use them to deliver encrypted ransomware. The attack methods can be roughly divided into the following methods: 1. Extensive vulnerability scanning . Using Nday vulnerabilities, 1day vulnerabilities, and 0day vulnerabilities to scan assets in batches is often referred to as…


Tackling Anti-Analysis Techniques of GuLoader and RedLine Stealer
https://unit42.paloaltonetworks.com/malware-configuration-extraction-techniques-guloader-redline-stealer/

Hackers target Apache RocketMQ servers vulnerable to RCE attacks
https://www.bleepingcomputer.com/news/security/hackers-target-apache-rocketmq-servers-vulnerable-to-rce-attacks/
