ROADtools Abuse Shows Cloud Identity Is the New Attack Surface
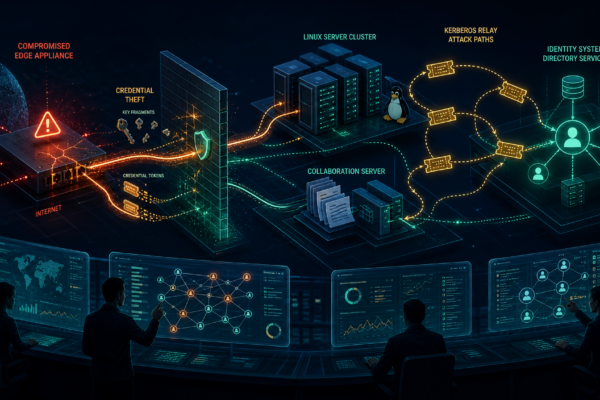
Unit 42’s ROADtools research shows why Microsoft Entra ID token abuse, rogue device registration, and Graph API enumeration need to be treated as core incident-response signals for SMBs and government contractors.